A recent statement from China left the Apple in trouble, again: Beijing government authorities have been using an advanced encryption-breaking tool, aimed at removing the anonymity of users of the AirDrop, the proprietary protocol for sharing content via Wi-Fi, present on iPhones, iPads, Macs, and other Apple devices. The method, aimed at identifying those who share subversive content (read criticism of the government and Prime Minister and General Secretary Xi Jinping), uses a flaw known to security professionals since 2019, which Apple was alerted to, but never corrected.
 Chinese authorities use AirDrop flaw to identify those who share subversive content (Credit: DALL-E) The Chinese government's statement was published last Monday (8), on the official page of the Department of Justice of Beijing City Hall. A local company called Wangshendongjian Technology has provided the means to identify and track users who have shared “inappropriate information” via AirDrop in public places such as stations and train carriages, using the setup that allows iPhone owners to receive files from anyone in their vicinity. nearby. By default, AirDrop was pre-configured to accept any connection, which activists and dissidents took advantage of to carry out digital protests. One of them was a digital reproduction of a physical protest, posters pasted in Beijing central on October 13, 2022, calling Ursi- say, Premier Xi a “despotic traitor”. The slogan caught on, outside and inside the country, being passed on via iPhones via wireless capability. Shortly afterwards, on November 9 of the same year, Apple implemented, through the iOS 16.1.1 update, a modification to the AirDrop configuration, changing the default state from “all” to “contacts only”. Apple never commented on why it made the change, but the timing suggests that the company may have been pressured by the Chinese government to do so. Now, local authorities claim that sharing of unsanctioned material in public places was still rampant, and to combat the practice and track down (and punish) those responsible, law enforcement officials announced the use of encryption-breaking and removal tools. of anonymity, exploiting a flaw made public in 2021. In this post, the Beijing Department of Justice says that iOS's protections regarding AirDrop, encryption and anonymization of users, have given many a feeling of security, enough that these forward dissenting materials. With this in mind, the 2019 flaw is being actively exploited.
Chinese authorities use AirDrop flaw to identify those who share subversive content (Credit: DALL-E) The Chinese government's statement was published last Monday (8), on the official page of the Department of Justice of Beijing City Hall. A local company called Wangshendongjian Technology has provided the means to identify and track users who have shared “inappropriate information” via AirDrop in public places such as stations and train carriages, using the setup that allows iPhone owners to receive files from anyone in their vicinity. nearby. By default, AirDrop was pre-configured to accept any connection, which activists and dissidents took advantage of to carry out digital protests. One of them was a digital reproduction of a physical protest, posters pasted in Beijing central on October 13, 2022, calling Ursi- say, Premier Xi a “despotic traitor”. The slogan caught on, outside and inside the country, being passed on via iPhones via wireless capability. Shortly afterwards, on November 9 of the same year, Apple implemented, through the iOS 16.1.1 update, a modification to the AirDrop configuration, changing the default state from “all” to “contacts only”. Apple never commented on why it made the change, but the timing suggests that the company may have been pressured by the Chinese government to do so. Now, local authorities claim that sharing of unsanctioned material in public places was still rampant, and to combat the practice and track down (and punish) those responsible, law enforcement officials announced the use of encryption-breaking and removal tools. of anonymity, exploiting a flaw made public in 2021. In this post, the Beijing Department of Justice says that iOS's protections regarding AirDrop, encryption and anonymization of users, have given many a feeling of security, enough that these forward dissenting materials. With this in mind, the 2019 flaw is being actively exploited.
Rainbow Connection
The method used by SHA-256 to identify who shared criticism of the Chinese government via AirDrop was not revealed, of course, but translations shared on the internet of the official statement point to an old concept in cryptography, rainbow tables. They are pre-computed tables, created to discover passwords by cracking hashes, in which such lists can contain billions and billions of entries. Because of this, they generally take up several terabytes of space. They were proposed in 1980, as a way to save the astronomical (for the time) use of computational power, to break layers of security. It works like this: let's say one of my passwords, the service doesn't matter, be it “cavalocorreto”, without the quotation marks. Using the MD5 encryption algorithm, it would be converted to the hash 2210B93C80A2899FCDE25ECF94D6BEE8. However, if this hash is thrown into a rainbow table that contains this combination, it will return the correct password to the hacker, or security professional linked to a government.
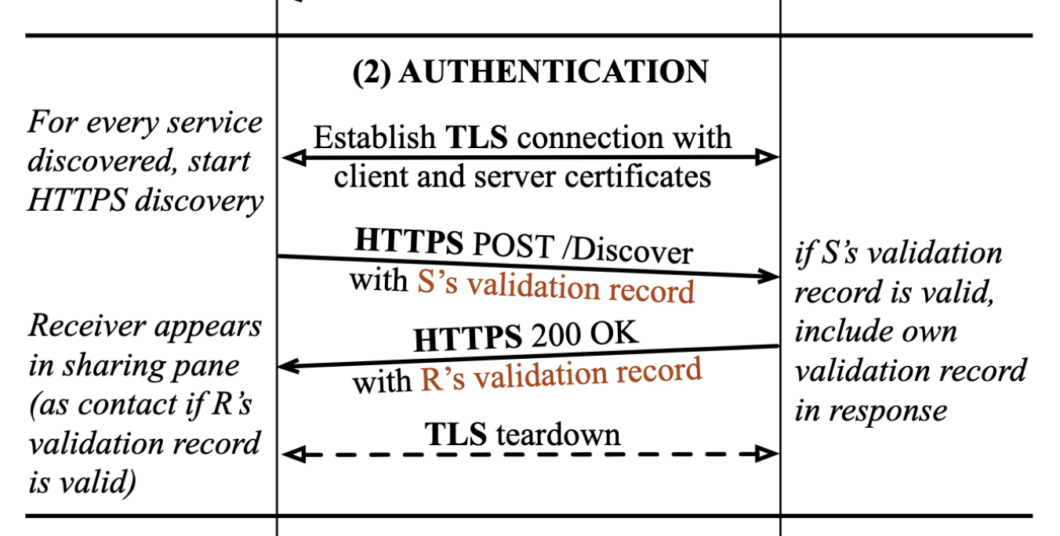 AirDrop discovery phase diagram (Credit: Heinrich et al/TU Darmstadt) AirDrop works by emitting (caution, PDF), via Bluetooth, the Apple ID identification hash of the iPhone sending the file, searching for others in the proximities that match the protocol requirements; if the email and number are also used as identifiers, each will have its own hash. If the receiver has configured his device to receive messages from anyone, the devices will initiate a handshake, where the call will be authenticated and they will exchange SHA-256 hashes between them. If the user has configured AirDrop to only receive requests from known contacts, the iPhone will ignore all attempts sent from unknown devices. Here's how the hacking method works: the tool collects open transmissions, throws them into its rainbow tables, and identifies the numbers and emails of users exchanging subversive materials. This happens because Apple does not “salt” hashes, where salt is a random string of characters, linked to a password, key or hash, that generates a new random hash with each new HTTPS POST request. Returning to the example given, with salt enabled, the hash linked to “cavalocorreto” would always continue to be the same, but each connection would generate a random secondary hash, making it impossible to reach the original, much less the password. AirDrop is not capable of using salt, so the hashes are subject to rainbow tables shared across the internet, of which the HashKiller service is one of the best known. A rainbow table is nothing more than a dictionary attack, more effective (in parts) than one that uses brute force, if we consider when the method was created and how limited PCs were then. Today, we have facilities powerful enough to run trial-and-error algorithms more efficiently, but having a list of hashes on hand is still simpler, especially since Apple hasn't done its part to increase AirDrop's security.
AirDrop discovery phase diagram (Credit: Heinrich et al/TU Darmstadt) AirDrop works by emitting (caution, PDF), via Bluetooth, the Apple ID identification hash of the iPhone sending the file, searching for others in the proximities that match the protocol requirements; if the email and number are also used as identifiers, each will have its own hash. If the receiver has configured his device to receive messages from anyone, the devices will initiate a handshake, where the call will be authenticated and they will exchange SHA-256 hashes between them. If the user has configured AirDrop to only receive requests from known contacts, the iPhone will ignore all attempts sent from unknown devices. Here's how the hacking method works: the tool collects open transmissions, throws them into its rainbow tables, and identifies the numbers and emails of users exchanging subversive materials. This happens because Apple does not “salt” hashes, where salt is a random string of characters, linked to a password, key or hash, that generates a new random hash with each new HTTPS POST request. Returning to the example given, with salt enabled, the hash linked to “cavalocorreto” would always continue to be the same, but each connection would generate a random secondary hash, making it impossible to reach the original, much less the password. AirDrop is not capable of using salt, so the hashes are subject to rainbow tables shared across the internet, of which the HashKiller service is one of the best known. A rainbow table is nothing more than a dictionary attack, more effective (in parts) than one that uses brute force, if we consider when the method was created and how limited PCs were then. Today, we have facilities powerful enough to run trial-and-error algorithms more efficiently, but having a list of hashes on hand is still simpler, especially since Apple hasn't done its part to increase AirDrop's security.
 Apple's billion-dollar deal with China gave it countless benefits; in return, the apple turns a blind eye to the government's demands (Credit: Reuters/Nikkei Asia)
Apple's billion-dollar deal with China gave it countless benefits; in return, the apple turns a blind eye to the government's demands (Credit: Reuters/Nikkei Asia)
Apple: “lalalá I don't hear anything…”
Basically, AirDrop leaks users' data not like a sieve, but like an open dam. Professionals who have access to rainbow tables and hash interception methods can convert the data into the personal information of anyone involved in the dissemination of protests and materials that the Chinese government does not want to spread. Here, the aim is to catch those who share them in the first place, those who pass them on, and those who received it, did not pass it on, but did not report to the authorities regarding the existence of dissident materials. According to Information Security researchers at the Technical University of Damrmstadt, in Germany, who published a study on the operation, and gross flaws, of AirDrop, Apple was alerted about the vulnerabilities in 2019, but never fixed it. Matthew Green, a cryptography expert at Johns Hopkins University in the United States, believes that Apple's inaction is due to technical difficulties; implementing the salt now would be a very complex task. On the other hand, it should be noted that Cupertino took a technically unrelated action shortly after the protests using its tool were revealed by The New York Times article. It is worth remembering that the company has a billion-dollar agreement with the local government, which resulted in benefits that no other company outside of País do Meio has, which allowed it to grow in the country; In return, Beijing has unrestricted access to iGadget users' data, in the form of a local iCloud. When contacted, Apple did not comment on the matter.
Bibliographic references
HEINRICH, A., HOLLICK, M., SCHNEIDER, T. et al. PrivateDrop: Practical Privacy-Preserving Authentication for Apple AirDrop. 30th USENIX Security Symposium, 19 pages, August 11-13, 2021. Available here. Source: Ars Technica
